
The Abstruse Case of Handling Kubernetes Security- Part 2
With so much complexity in deploying Kubernetes, unwanted exposure tends to increase, making Kubernetes vulnerable to security threats and unauthorized

With so much complexity in deploying Kubernetes, unwanted exposure tends to increase, making Kubernetes vulnerable to security threats and unauthorized

Enterprises, in the continuous efforts to strengthen their cloud-native strategies, including what platforms and tools they should use may benefit
Monitoring in DevOps brings significant benefits to enterprises but only when it is effectively implemented. Here are 5 best use
Here’s how you can devise an efficacious DevOps monitoring strategy in a rapidly changing environment for your enterprise. Look at
Here, in this blog, we’ll talk about what is DevOps monitoring, what are the different types of monitoring in DevOps,
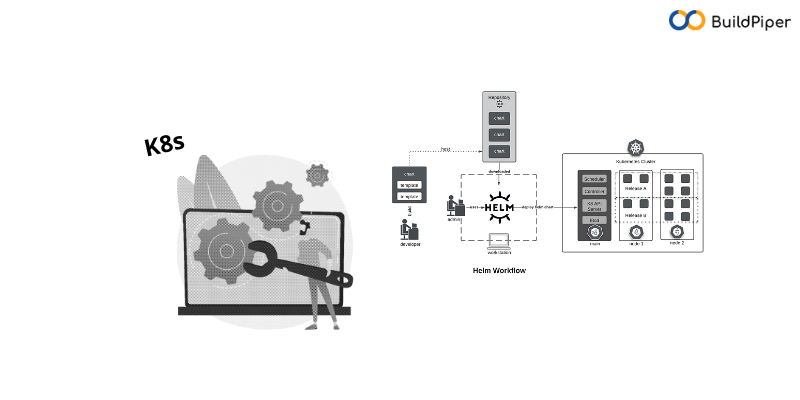
Here, we’ll now talk about a newly added feature in BuildPiper: the Kubernetes & Microservices delivery platform. So here’s how